MFA / 2FA Implementation
Microsoft 365 Backup and Hardened security with Multi Factor Authentication.

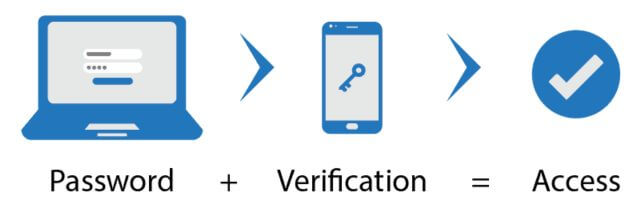
MFA Multi Factor Authentication
The clue is in the name and provides a second level of security to a device only you have access to, your Mobile Phone.
There is no MFA solution that can’t be hacked. Anyone claiming that their solution is unhackable is either lying to you or naive.
MFA provides a secondary perimeter of security making it more difficult to hack your account but not impossible.
They are not Interested In Me!

Sorry to burst any bubbles but “they” are.
The current vogue is to to deploy Ransomware. The encryption of data requesting a Ransom is Paid to unlock data.
You need to make it as difficult as possible for criminals to access or steal your data. Multi Factor or 2 Factor Authentication is a step in the right direction.
Add the misconception that Data Transferred to the Cloud does not need to be backed up. This will cost you or your business.
Complex Passwords are a good policy to adopt but how complex are yours?
Every time you sign in to an untrusted device while you have two-step verification turned on, you’ll get a security code in email or on your phone, making sure you are you.
It is always worthwhile bringing this subject to the foreground. “How secure is your password?”
I have distributed previously and spoken to clients regarding the importance of secure Passwords.
As we more more and more to online services Microsoft 365 and Browser Delivered applications Passwords alone do not provide the level of security necessary.
Here are my comments previously:
We all know that using birthdates, a child’s name or a pets name is a recipe for disaster. Using simple brute force tactics passwords of this nature can be guessed or gleaned from social network pages such as Facebook. Also using passwords which have less than 8 characters makes the task easier to hack into any of your accounts.
I appreciate remembering a random string of characters is not easy however there are ways to remember. You can make a password memorable to you and hide the true meaning to a third party viewing it. I touched on the use of names and birthdates. You can use these if you mix things up.
Example
Ben was born on the 1st June 1979. He decides on a password of 01061979. This would be an easy password to attack and succeed (0.025 seconds) using brute force. In this case a hacker would start at 00000000 through to 99999999.
Too weak for a password he decides ben01061979. This now has a good long password, greater than 8 characters, and would take 12 months to crack – potentially. A little knowledge would start an undesirable to use his name and birthdate and may crack this password in less time.
Uppercase and lowercase. Using a password along the same scheme we can look at Ben01061979. This has the potential of taking 412 years to brute force attack however a little knowledge of Ben and we could reduce this considerably.
Don’t forget /?!#- Adding any of these characters to a passwords greatly reduces the chance of a password being cracked. Ben01061979! Shows a potential time of 344,000 years.
And More
Let’s stretch this out further. 1t 1s n0t D1ff1cult to mak3 a pa55word hard t0 crack 0r gu355. I am hoping you get the idea. Therefore if we take the last iteration of password and apply the same rules, B3nO1O61979! We can see that the password would be difficult to guess, only Ben knows the rules how the password is made, it is 12 characters long and difficult to guess even with knowledge of Ben and his birthday. This also shows a value of 344,000 years to crack which is no improvement however knowledge of Ben and his birth date is obscured within to protect against guesses.
The time taken to crack passwords are obtained from www. howsecureismypassword.net
Play with your current passwords, the website does not capture or keep any data inserted.
MFA / 2FA What is it?
Two-factor authentication (2FA) is a security process in which a user is only granted access to a system after successfully presenting two different types of evidence to an authentication mechanism — typically something they know (e.g., a password) and something they have (e.g., a security token).
MFA is significantly more secure than traditional single-factor authentication (SFA) methods, such as passwords alone. This is because it makes it much more difficult for attackers to gain unauthorized access to systems and data, even if they have stolen a user’s password.
For example, if an attacker steals a user’s password for a website, they will still be unable to access the account if they do not also have access to the user’s MFA device. This is because the attacker will not be able to enter the code that is generated by the MFA device.
MFA is a very effective security measure, and it is highly recommended that all small businesses implement it. MFA can help to protect your business from a wide range of cyberattacks, including phishing, password spraying, and brute force attacks.
In addition to being more secure, MFA is also relatively easy to implement. Most major websites and applications now support MFA, and there are a number of free and paid Multi Factor solutions available.
Overall, 2FA is a very cost-effective and easy-to-implement security measure that can provide a significant boost to the security of your small business.
Here are some of the benefits of using Multi Factor for small businesses:
- Increased security: MFA adds an extra layer of security to your systems and data, making it much more difficult for attackers to gain unauthorized access.
- Reduced risk of data breaches: MFA can help to prevent data breaches by making it more difficult for attackers to steal passwords and other sensitive information.
- Improved compliance: Many industry regulations, such as HIPAA and PCI DSS, require businesses to implement strong security measures, such as Multi Factor.
- Increased customer trust: Customers are more likely to trust businesses that take security seriously. By implementing MFA, you can show your customers that you are committed to protecting their data.
If you are a small business owner, I encourage you to consider implementing Multi Factor. It is a simple and effective security measure that can help to protect your business from a variety of cyberattacks.
Contact us today and see how we can help you and your business be more successful




